FAQ
Everything You Want to Know

Outbound Connectivity Requirements
- 8.8.8.8 (DNS)
- checkip.amazonaws.com (HTTPS) (External IP address – HTTPS)
- mirrors.ocf.berkeley.edu (Ubuntu updates from US repo)
- stingbox.twocyber.com (HTTPS)
Inbound Requirements
- None – device is a honeypot and will alert on inbound connection requests
You can force StingBox to use a custom DNS server by changing a file named “resolv.txt.unset” on the SD card of your StingBox.
This file will only be on your SD card if your StingBox is running software version 1.95 or greater.
If you have an older StingBox, you can obtain this by simply connecting your StingBox to a DHCP network for 10 minutes to download and install the update.
Instructions for setting a custom DNS server on a physical StingBox can be found in the “readme.txt” file or below:
Very Important: After you change the file according to instructions below, you will need to allow StingBox to boot with the new settings you have added. Then, you must wait 10 minutes to give StingBox time to load and connect. Then you must unplug power and reboot again.
Using a text editor, edit resolv.txt.unset, save the file and rename it from resolv.txt.unset to resolv.txt
The file should only have one line in it with the nameserver you specify after the word nameserver. Like the below.
nameserver 8.8.8.8
You can assign an IP to StingBox by changing a file named “eth0.txt.unset” on the SD card of your StingBox.
This file will only be on your SD card if your StingBox is running software version 1.59 or greater.
If you have an older StingBox, you can obtain this by simply connecting your StingBox to a DHCP network for 10 minutes to download and install the update.
Instructions for setting the IP on a physical StingBox can be found in the “eth0.txt.unset” file or below:
Very Important: After you change the file according to instructions below, you will need to allow StingBox to boot with the new settings you have added. Then, you must wait 10 minutes to give StingBox time to load and connect. Then you must unplug power and reboot again.
Using a text editor, hash the DHCP section below and unhash the Static IP section. You must know and properly configure your desired IP address, netmask, gateway and nameserver.
Save the file, and rename it from eth0.txt.unset to eth0.txt
#configuration for DHCP auto eth0 iface eth0 inet dhcp #configuration for Static IP. Uncomment (remove the # from the 6 lines below to use, and add # to the two lines above) # auto eth0 # iface eth0 inet static # address 192.168.0.158 # netmask 255.255.255.0 # gateway 192.168.0.1 # dns-nameservers 8.8.8.8 #To have the stingbox use this file to configure the network adapter #You must rename the file from eth0.txt.unset to eth0.txt #once this change is made, do not delete eth0.txt #after changing this file, unplug and plug back in your stingbox (wait 3 minutes) and #then unplug and plug back in your stingbox.
Plug your StingBox into the power outlet and any open port on your network. Create an account and enter the code printed on your StingBox and your subscription code from your purchase. That’s it! More help is available at https://www.stingbox.com/setup/
Connectivity Issue Troubleshooting
-
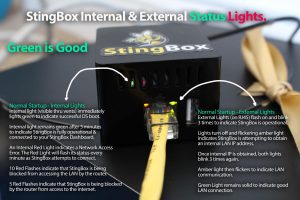
Make sure your StingBox is physically plugged into power and has established an ethernet physical connection and received an IP address from your DHCP server (if you need to set up a static IP address, instructions are here, if you need to specify a DNS server, instructions are here). You can determine a network connection has occurred by looking at the lights inside the StingBox while it boots up.

- Check your power supply to ensure it is providing your StingBox.
- Check your network cable is plugged in and the port it is connected to is clean.
- Sometimes the SD card gets jostled free if the stingbox is handled roughly. Power off, unplug and plug-in the SD card then power it back on.
- Check to ensure your network and your StingBox are able to connect to cloud services used by StingBox. Sometimes networks, web gateways or proxies block a StingBox from contacting its cloud services. If you block all services by default, you need to enable/whitelist these services for your StingBox.
Outbound Connectivity Requirements
- stingbox.twocyber.com (HTTPS)
- 8.8.8.8 (DNS)
- checkip.amazonaws.com (HTTPS)
- mirrors.ocf.berkeley.edu (Ubuntu updates from US repo)
- If you are having intermittent connectivity issues, you can check your stingbox connectivity manager on your dashboard to see a full log of events with your StingBox including every check-in.
StingBox has a opt-in feature which scans for open SMB shares. You’ve enabled this and StingBox is attempting to authenticate to a share on your network with 'root' as username and a blank password. Sometimes network monitoring tools will alert on this activity. You can disable open SMB share scanning on your StingBox device settings page.
Ideal locations include – directly to a port on your router, into a network switch or into an open jack which plugs into your router.
StingBox offers WebHook and Syslog alert types. Most SIEMs are able to consume these alerts. For more information, please see our help articles on these alert types.
Additionally, many customers have implemented SIEM integration through a periodic pull from our API. StingBox API Documentation.
If this method does not work for you, please email us at support@stingbox.com and we can get things set up.
To WhiteList an IP (for example, from a network vulnerability scanner), first go to your StingBox Dashboard and click on Add/Manage StingBox section. Next, look for the “WhiteList IP Manager” link on the bottom of the StingBox you want to stop sending alerts when hit by a particular IP. Next, Add the IP and Name the Machine for easier identification.
Yes, StingBox and FireWalla are compatible. StingBox is a honeypot device while FireWalla is a firewall device.
Network professionals can now receive Stingbox alerts via Syslog. Currently, sending is performed only via the TCP protocol.
To set up receiving alerts using syslog, you need to configure your server to receive such logs using the TCP protocol. Next, go to the stingbox website and go to the alert methods management page. There you will see this new option at the bottom:

To start receiving syslog alerts, you need to specify here the IP address of your server to which the alerts will be sent, as well as the port used. Follow the format specified in this field: <ip>:<port>
So if you did everything right and entered the correct address, you will receive alerts to this server. Here’s what such notifications look like:

Messages comply with the CEF format. This format implies the following data set:
CEF:Version – CEF version
|Device Vendor – StingBox
|Device Product – the code of your StingBox from which the message was received
|Device Version – your StingBox software version
|Signature ID – unique alert hash
|Name – this is the alert message itself
|Severity – message severity, from 0 (debug) to 7 (emergency)
More information on the CEF format can be found here: CEF WhitePaper
We’d love to figure out how to make you successful with StingBox. Please email us any questions to us at support@stingbox.com. If you just want to cancel, instructions are here: https://www.stingbox.com/cancel
Yes. StingBox has undergone penetration testing with clean results. We offer results of our penetration during pre-sales and customer discovery if needed. Please email support@stingbox.com.
No. StingBox HoneyPots are designed to detect network intruders, similar to a building alarm system which does not stop burglars but only detects them. Detection informs and enables response. Improving detection is a critical part of a complete, Protection, Detection and Response plan which can stop hackers from winning this battle.
No, StingBox is a honeypot, not a 100% guarantee you have not been hacked. If an attacker stays on a single host on your network it is likely that StingBox will not detect the attacker (however, we may have detected the attacker when they were trying to compromise that first host). We suggest having endpoint security for the devices on your network in addition to the StingBox.
We only offer StingBox through a subscription.
StingBox is a cloud-delivered subscription service with an optional hardware component. We continually add capabilities and features to StingBox (discovery scanning, open port alerts, hackercam, etc) and our dashboard and alerting services. Additionally, we provide extensive support for our customers.
Our subscription model makes StingBox a sustainable business.
DIY honeypots information can be found here
The StingBox HackerCam feature records a hackers keystrokes and then send those to you as a follow-up to the the initial alert that your StingBox HoneyPot has been probed.
To test this feature, you can pretend to be a hacker. A typical network intruder will have run an NMap scan on your network to identify interesting targets and will see the custom hostname you have given your StingBox and that it has open ports to probe with a password cracker. Both activities that will trigger an initial StingBox Alert.
The next step would be for the hacker to SSH the StingBox. They will now know the IP address of the Stingbox. You copy this next step using any SSH program like Putty for Windows or Termius for IOS.
You’ll enter (replace Xs with your StingBox IP address:
You may need to specify additional info in your SSH client like the following:
ssh -oHostKeyAlgorithms=+ssh-rsa -oPubkeyAcceptedAlgorithms=+ssh-rsa root@XXX.XXX.XXX.XXX
You’ll be prompted for a password and you can enter anything. Click enter and you will be seeing what a hacker would see who believes they have successfully gained root access to a machine on your network.
StingBox will mimic standard server responses to any standard Linux command. You can (pretend to) download a hacker kit from GitHub or type anything and hackercam will record it and send this in an alert as a link you can click to watch or share.
No, but we have tested an inexpensive adapter that we can recommend. POE Texas’ Adapter can be purchased directly at POETexas.com or from Amazon.
Note: It’s important to order the Micro USB version. This adapter has also changed connectors since our initial purchase. You may want to consider the UCTronics adapter below. One of two of these POE Texas adapters we tested failed after 9 months. The other is still running since May of 2000. Full disclosure: The adapter failed while powering an alternative StingBox platform we were testing. The platform still works, but the POE doesn’t. This isn’t a sufficient data set to say for certain that the power supply was the cause of its failure.
There are several other manufacturers on Amazon 7/2022
Update. StingBox customers are giving positive reviews of this POE splitter from UCTronics
We work with MSPs, MSSPs, IT professionals, VARs, distributors, and solution providers in a variety of models – please email us at sales@stingbox.com to start a conversation. We do not currently work with digital-only drop-shippers.
Please email support@stingbox.com and we can help you do this. Hosts will also automatically drop out of recent hosts in 24 hours.
Click “account settings” and then complete the password reset form to reset your password. If you can’t access your account, please email support@stingbox.com
We are using a version of the PI Architecture with 512mb of RAM running an ARM linux operating system.
If you recently connected a device to your network yourself there is nothing to worry about as it was an expected new device connection.
If you can’t figure out what the new device is on your network or why it was installed (i.e. someone you don’t know is using your Wi-Fi connection), you may want to block the device (i.e. on your router).
No, Stingbox is not a NIPS (network intrusion prevention system) – just a Honeypot.
To set up receiving alerts via Webhooks, you need to add the desired URL to which alerts will be sent on the “Alert Settings” page of your Dashboard
A request will be sent to the received URL every time any alert is triggered (according to the configured severity). The request will always be sent using the POST method, the body of which will contain JSON data about the alert. The request will always be sent only once, without repeats (if your server cannot process it). There are currently no restrictions on the protocol used, so you can use https or http. Here is an example of the JSON structure:

Field Detail:
- severity: text information about the importance of the alert. The following are currently available: Info, Important, Critical
- message: content message of alert
- timestamp: time stamp at which the alert was triggered
- stingbox_code: unique stingbox code
- stingbox_name: the name of the stingbox (by default, it is equal to stingbox_code)
- stingbox_software_version: version of the installed stingbox software
- cef: messages in CEF format. More details can be found here
Please contact us at support@stingbox.com and we can help you authenticate to your account.
Yes, just enter them on the “manage alerts” page.
Yes. Documentation for StingBox’s API is at StingBox API Documentation
Stingbox performs a ping Scan and an arp-scan on the local network to which it is assigned an IP address from a DHCP server.
Yes. StingBox’s dashboard supports grouping StingBoxes and defining custom alerts types and methods for each group
StingBox does not support multiple network interfaces.
StingBox virtual currently does not support multiple network interfaces.
You can change the alert settings from your dashboard. There are three categories of alert. Critical, Important and Informational. Each can be set with it’s own unique instructions for how and where to send alerts. You can also always disable any alert methods from your dashboard. You may also consider whitelisting specific IP addresses which cause excessive alerts (i.e. known vulnerability scanners)
Open up any web browser on your local network and enter ftp://YOURSTINGBOXIP into the url bar. Example (ftp://192.168.1.29). You can find your STINGBOXIP on your dashboard. This will generate an alert for an attempted FTP scan attempt.
StingBox collects and stores
- Attack sessions from attackers (what they typed, how they interacted with the honeypot)
- IP address of your external network interface
- Open ports on your external network interface
- If you have worked with support to enable Lan Scanning – Names and MAC addresses of devices on your network which StingBox discovers with a network scan
This information is sent over an encrypted channel back to StingBox’s cloud servers so you can review this information on your dashboard.
As long as the StingBox is reachable by attackers, it will perform its honeypot functions. Functionality does not change based on the network configuration.
You can change your payment details on your Stripe Dashboard Here.
If you have a subscription through PayPal, or an invoice based subscription please email support@stingbox.com and we can update your info.
No, as long as the StingBox is reachable by attackers, it will perform its honeypot functions. You may choose to deploy multiple StingBox on different segments of your network to create more possible points of detection.
Yes, the StingBox is hardened against attacks and does not cause excessive network traffic.
StingBox does not support changing the network discovery scanning interval.
Occasionally an IP address or MAC address will change on your network, in these cases, the host may appear multiple times on your StingBox dashboard.
Yes, we are able to ship for annual subscriptions only.
Your StingBox will show as connected on your dashboard.
StingBox was designed to be a low cost solution to a tough problem, detecting if someone is snooping on your network. We are able to maintain low costs because of our Software as a Service model and our low cost hardware design.
Every 5 minutes.
Every 10 minutes.
StingBox has an optional feature to perform network scanning which may trigger other network monitoring software. You can enable/disable this feature on your dashboard.
Yes, StingBox is available for installation on the cloud or an existing machine. More information on StingBox Virtual can be found here.
You can force StingBox to use a custom DNS server by changing a file named “resolv.txt.unset” on the SD card of your StingBox.
This file will only be on your SD card if your StingBox is running software version 1.95 or greater.
If you have an older StingBox, you can obtain this by simply connecting your StingBox to a DHCP network for 10 minutes to download and install the update.
Instructions for setting a custom DNS server on a physical StingBox can be found in the “readme.txt” file or below:
Very Important: After you change the file according to instructions below, you will need to allow StingBox to boot with the new settings you have added. Then, you must wait 10 minutes to give StingBox time to load and connect. Then you must unplug power and reboot again.
Using a text editor, edit resolv.txt.unset, save the file and rename it from resolv.txt.unset to resolv.txt
The file should only have one line in it with the nameserver you specify after the word nameserver. Like the below.
nameserver 8.8.8.8
You can assign an IP to StingBox by changing a file named “eth0.txt.unset” on the SD card of your StingBox.
This file will only be on your SD card if your StingBox is running software version 1.59 or greater.
If you have an older StingBox, you can obtain this by simply connecting your StingBox to a DHCP network for 10 minutes to download and install the update.
Instructions for setting the IP on a physical StingBox can be found in the “eth0.txt.unset” file or below:
Very Important: After you change the file according to instructions below, you will need to allow StingBox to boot with the new settings you have added. Then, you must wait 10 minutes to give StingBox time to load and connect. Then you must unplug power and reboot again.
Using a text editor, hash the DHCP section below and unhash the Static IP section. You must know and properly configure your desired IP address, netmask, gateway and nameserver.
Save the file, and rename it from eth0.txt.unset to eth0.txt
#configuration for DHCP auto eth0 iface eth0 inet dhcp #configuration for Static IP. Uncomment (remove the # from the 6 lines below to use, and add # to the two lines above) #auto eth0 #iface eth0 inet static # address 192.168.0.158 # netmask 255.255.255.0 # gateway 192.168.0.1 # dns-nameservers 8.8.8.8 #To have the stingbox use this file to configure the network adapter #You must rename the file from eth0.txt.unset to eth0.txt #once this change is made, do not delete eth0.txt #after changing this file, unplug and plug back in your stingbox (wait 3 minutes) and #then unplug and plug back in your stingbox.
Outbound Connectivity Requirements
- 8.8.8.8 (DNS)
- checkip.amazonaws.com (HTTPS) (External IP address – HTTPS)
- mirrors.ocf.berkeley.edu (Ubuntu updates from US repo)
- stingbox.twocyber.com (HTTPS)
Inbound Requirements
- None – device is a honeypot and will alert on inbound connection requests
Connectivity Issue Troubleshooting
Make sure your StingBox is physically plugged into power and has established an ethernet physical connection and received an IP address from your DHCP server (if you need to set up a static IP address, instructions are here, if you need to specify a DNS server, instructions are here). You can determine a network connection has occurred by looking at the lights inside the StingBox while it boots up.
- Check your power supply to ensure it is providing your StingBox.
- Check your network cable is plugged in and the port it is connected to is clean.
- Sometimes the SD card gets jostled free if the stingbox is handled roughly. Power off, unplug and plug-in the SD card then power it back on.
- Check to ensure your network and your StingBox are able to connect to cloud services used by StingBox. Sometimes networks, web gateways or proxies block a StingBox from contacting its cloud services. If you block all services by default, you need to enable/whitelist these services for your StingBox.
Outbound Connectivity Requirements
- stingbox.twocyber.com (HTTPS)
- 8.8.8.8 (DNS)
- checkip.amazonaws.com (HTTPS)
- mirrors.ocf.berkeley.edu (Ubuntu updates from US repo)
- If you are having intermittent connectivity issues, you can check your stingbox connectivity manager on your dashboard to see a full log of events with your StingBox including every check-in.
Many customers have implemented SIEM integration through a periodic pull from our API. StingBox API Documentation If this method does not work for you, please email us at support@stingbox.com and we can get things set up.
To WhiteList an IP (for example, from a network vulnerability scanner), first go to your StingBox Dashboard and click on Add/Manage StingBox section. Next, look for the “WhiteList IP Manager” link on the bottom of the StingBox you want to stop sending alerts when hit by a particular IP. Next, Add the IP and Name the Machine for easier identification.
We’d love to figure out how to make you successful with StingBox. Please email us any questions to us at support@stingbox.com. If you just want to cancel, instructions are here: https://www.stingbox.com/cancel
Ideal locations include – directly to a port on your router, into a network switch or into an open jack which plugs into your router.
Yes. StingBox has undergone penetration testing with clean results. We offer results of our penetration during pre-sales and customer discovery if needed. Please email support@stingbox.com.
Go to your Discovered Hosts page from your StingBox dashboard to learn more about hosts on your network (i.e. Hostname, manufacturer or a custom name you’ve given the host in the past)
We work with MSPs, MSSPs, IT professionals, VARs, distributors, and solution providers in a variety of models – please email us at sales@stingbox.com to start a conversation. We do not currently work with digital-only drop-shippers.
StingBox has a opt-in feature which scans for open SMB shares. You’ve enabled this and StingBox is attempting to authenticate to a share on your network with a blank username and password. Sometimes network monitoring tools will alert on this activity. You can disable open SMB share scanning on your StingBox device settings page.
Yes, just enter them on the “manage alerts” page.
Yes. Documentation for StingBox’s API is at StingBox API Documentation
Please email support@stingbox.com and we can help you do this. Hosts will also automatically drop out of recent hosts in 24 hours.
Plug your StingBox into the power outlet and any open port on your network. Create an account and enter the code printed on your StingBox and your subscription code from your purchase. That’s it! More help is available at https://www.stingbox.com/setup/
Click “account settings” and then complete the password reset form to reset your password. If you can’t access your account, please email support@stingbox.com
If you recently connected a device to your network yourself there is nothing to worry about as it was an expected new device connection.
If you can’t figure out what the new device is on your network or why it was installed (i.e. someone you don’t know is using your Wi-Fi connection), you may want to block the device (i.e. on your router).
Honeypot Functionality: As long as StingBox is routable from your VLAN's it will act as a honeypot and respond to requests. Ensure there are routes to your StingBox to catch hackers.
Host Discovery: StingBox has support for multiple VLANS with a single subscription. Simply specify the IP ranges on your dashboard and the sting box will do device discovery on all of your VLANS. Please note, MAC address discovery only works on the local network upon which StingBox is deployed.
We only offer StingBox through a subscription.
StingBox is a cloud-delivered subscription service with an optional hardware component. We continually add capabilities and features to StingBox (discovery scanning, open port alerts, hackercam, etc) and our dashboard and alerting services. Additionally, we provide extensive support for our customers.
Our subscription model makes StingBox a sustainable business.
DIY honeypots information can be found here
StingBox does a best-effort scan of your network using ping and arp-discovery approaches every 10 minutes.
Troubleshooting:
- Please make sure you have waited 10 minutes for the StingBox to scan your network. Your network may be in different segments and, by default StingBox is only able to scan the segment upon which it connected. You may configure custom discovery scanning ranges on your dashboard.
- Ensure you have device scanning enabled on your StingBox settings.
- Ensure your network allows devices the ability to ping hosts on the same network. Sometimes networks block ping scans — the method used by StingBox to do best-effort device discovery.
Please contact us at support@stingbox.com and we can help you authenticate to your account.
No, but we have tested an inexpensive adapter that we can recommend. POE Texas’ Adapter can be purchased directly at POETexas.com or from Amazon.
Note: It’s important to order the Micro USB version. This adapter has also changed connectors since our initial purchase. You may want to consider the UCTronics adapter below. One of two of these POE Texas adapters we tested failed after 9 months. The other is still running since May of 2000. Full disclosure: The adapter failed while powering an alternative StingBox platform we were testing. The platform still works, but the POE doesn’t. This isn’t a sufficient data set to say for certain that the power supply was the cause of its failure.
There are several other manufacturers on Amazon 7/2022
Update. StingBox customers are giving positive reviews of this POE splitter from UCTronics
Yes. StingBox’s dashboard supports grouping StingBoxes and defining custom alerts types and methods for each group
StingBox does not support multiple network interfaces.
StingBox virtual currently does not support multiple network interfaces.
You can change the alert settings from your dashboard. There are three categories of alert. Critical, Important and Informational. Each can be set with it’s own unique instructions for how and where to send alerts. You can also always disable any alert methods from your dashboard. You may also consider whitelisting specific IP addresses which cause excessive alerts (i.e. known vulnerability scanners)
Open up any web browser on your local network and enter ftp://YOURSTINGBOXIP into the url bar. Example (ftp://192.168.1.29). You can find your STINGBOXIP on your dashboard. This will generate an alert for an attempted FTP scan attempt.
We are using a version of the PI Architecture with 512mb of RAM running an ARM linux operating system.
Stingbox performs a ping Scan and an arp-scan on the local network to which it is assigned an IP address from a DHCP server. Additionally, custom ranges can be defined through the dashboard.
No, StingBox is a honeypot, not a 100% guarantee you have not been hacked. If an attacker stays on a single host on your network it is likely that StingBox will not detect the attacker (however, we may have detected the attacker when they were trying to compromise that first host). We suggest having endpoint security for the devices on your network in addition to the StingBox.
No, as long as the StingBox is reachable by attackers, it will perform its honeypot functions. You may choose to deploy multiple StingBox on different segments of your network to create more possible points of detection.
Stingbox has support for multiple VLANS with a single subscription. Simply specify the IP ranges on your dashboard and the sting box will do device discovery on all of your VLANS.
Yes, StingBox and FireWalla are compatible. StingBox is a honeypot device while FireWalla is a firewall device.
Yes, the StingBox is hardened against attacks and does not cause excessive network traffic.
StingBox does not support changing the network discovery scanning interval.
Go to your Discovered Hosts page from your StingBox dashboard to learn more about hosts on your network (i.e. Hostname, manufacturer or a custom name you’ve given the host in the past)
No. StingBox HoneyPots are designed to detect network intruders, similar to a building alarm system which does not stop burglars but only detects them. Detection informs and enables response. Improving detection is a critical part of a complete, Protection, Detection and Response plan which can stop hackers from winning this battle.
Occasionally an IP address or MAC address will change on your network, in these cases, the host may appear multiple times on your StingBox dashboard.
Yes, we are able to ship for annual subscriptions only.
Your StingBox will show as connected on your dashboard.
StingBox was designed to be a low cost solution to a tough problem, detecting if someone is snooping on your network. We are able to maintain low costs because of our Software as a Service model and our low cost hardware design.
Every 5 minutes.
Every 10 minutes.
StingBox has an optional feature to perform network scanning which may trigger other network monitoring software. You can enable/disable this feature on your dashboard.
StingBox collects and stores
- Attack sessions from attackers (what they typed, how they interacted with the honeypot)
- IP address of your external network interface
- Open ports on your external network interface
- Names and MAC addresses of devices on your network which StingBox discovers with a network scan
This information is sent over an encrypted channel back to StingBox’s cloud servers so you can review this information on your dashboard.
Yes, StingBox is available for installation on the cloud or an existing machine. More information on StingBox Virtual can be found here.
Stingbox has support for multiple VLANS with a single subscription. Simply specify the IP ranges on your dashboard and the sting box will do device discovery on all of your VLANs
As long as the StingBox is reachable by attackers, it will perform its honeypot functions. Functionality does not change based on the network configuration.
Remember to set your custom network discovery ranges in your dashboard if you do this.
You can change your payment details on your Stripe Dashboard Here.
If you have a subscription through PayPal, or an invoice based subscription please email support@stingbox.com and we can update your info.
No, Stingbox is not a NIPS (network intrusion prevention system) – just a Honeypot.
